The credentials were correct. The Google account was active. The login still failed.
Not with a clear error message. Not with a server notice. Just a loop — the sign-in screen reloading, the spinner appearing, the redirect going nowhere. Anyone who has tried to access MagicSchool AI through a school-managed Google Workspace account has likely hit this exact wall. The instinct is to blame a wrong password, a slow server, or a platform outage. That instinct is almost always wrong.
The actual problem sits one layer upstream, in a place most educators never think to look.
What the Login Loop Is Actually Telling You
When MagicSchool login fails silently — no error, no explanation, just a redirect that goes nowhere — the browser is not confused about who you are. It already knows. The problem is that it cannot prove that identity to a third-party service because your school’s network policy will not allow it.
School districts running Google Workspace for Education operate under strict IT governance. Those policies frequently include a setting that blocks third-party cookies at the browser or domain level. Third-party cookies are not tracking cookies in the consumer sense. In the context of Single Sign-On, they are the communication layer that allows a service like MagicSchool to confirm your Google identity after the redirect.
When that layer is blocked, the handshake never completes. Google confirms your identity on its end. MagicSchool never receives the confirmation. The browser loops back to the start. From the user’s perspective, nothing happened. From the system’s perspective, the authentication token was silently discarded.
This is not a MagicSchool server problem. It is an identity handshake problem caused by your school’s cookie policy.
The Wrong Diagnosis That Wastes the Most Time
The first assumption is always the password. The second is usually the platform. Educators check the MagicSchool AI status page, look for reported outages, try a different browser, clear their cache, and attempt the login again. Some submit a support ticket describing a login failure that sounds like a server error.
None of those steps address the actual cause. The platform may be running perfectly. The Google account may be fully active. The browser cache may be clean. None of that matters if the school domain policy is intercepting the authentication token before MagicSchool can read it.
The Hidden Workload
Every failed login attempt that gets misdiagnosed as a password error or server outage creates a secondary workload: support tickets, IT escalations, and lost planning time. The real cost is not the five minutes spent on the login screen. It is the hour spent in the wrong diagnostic channel because the actual cause — a cookie policy — never appeared in the error message.
The pattern here is consistent across managed education environments. The error is invisible. The cause is structural. And the fix requires touching a setting that most educators do not know exists.
How SSO Actually Works — and Where It Breaks for School Accounts
Single Sign-On is designed to reduce friction. Instead of creating a separate username and password for every tool, you authenticate once through a central provider — in most school cases, Google — and that verified identity is passed to other services. It works smoothly when all the components can communicate.
The sequence for MagicSchool looks roughly like this:
- You click “Sign in with Google” on MagicSchool.
- Your browser redirects to Google’s authentication server.
- Google verifies your school account credentials.
- Google issues an authentication token and sends it back to MagicSchool via a redirect URL.
- MagicSchool reads that token, confirms your identity, and opens your account.
Step 4 is where school domain policies interfere. The authentication token travels as part of a cross-site request. If the browser or the school’s proxy layer treats that cross-site request as a blocked third-party interaction, the token is dropped before MagicSchool ever receives it.
The result is that Google successfully authenticated you, but MagicSchool received nothing. The redirect loop is not a bug. It is the browser faithfully following a policy that was never intended to block legitimate education tools — but does anyway.
Before and After: What the Broken and Working States Look Like
BEFORE — Broken State
Login attempt via school Google account → Google authentication completes → redirect back to MagicSchool → browser drops the authentication token (third-party cookie blocked) → MagicSchool receives nothing → login screen reloads with no error message → educator assumes wrong password or server fault → time lost in wrong diagnosis channel.
AFTER — Working State
Browser cookie settings updated to allow third-party cookies for MagicSchool domain → login attempt via school Google account → Google authentication completes → authentication token passes through → MagicSchool receives and reads the token → account opens without a loop → login friction resolved in a single session.
The shift between these two states does not require IT department involvement in every case. For educators who have browser-level access, the fix can often be made directly. For those on fully locked-down managed devices, IT coordination is the right path — but knowing the exact cause makes that conversation roughly ten times faster than reporting a vague “login not working” ticket.
The Practical Fix: Cookie Exceptions for the MagicSchool Domain
The resolution depends on where the cookie block is enforced. There are three common scenarios in school environments:
Scenario 1: Browser-level block (most common for individual educators)
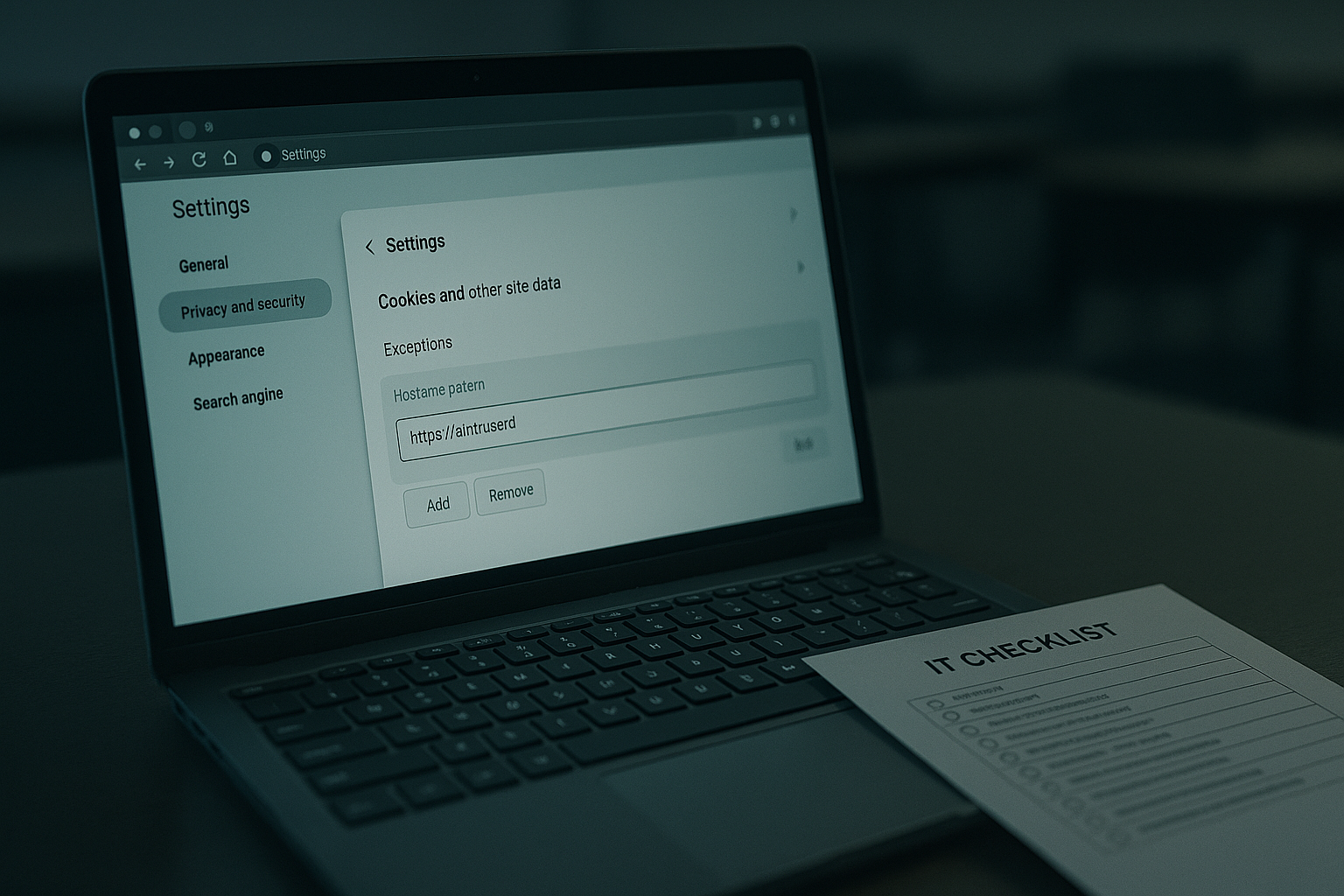
In Chrome, navigate to Settings → Privacy and Security → Third-party cookies. Look for the option to add site exceptions. Add the MagicSchool domain (magicschool.ai) as an allowed site. This creates a specific exception without disabling cookie protection across the entire browser.
In Firefox, the equivalent path is Settings → Privacy and Security → Enhanced Tracking Protection → Manage Exceptions. Add the MagicSchool sign-in URL to the exceptions list.
Scenario 2: School-managed Chrome policy (requires IT)
If the device is managed through Google Admin Console, the cookie policy may be set at the organizational unit level. An IT administrator can add MagicSchool to the CookiesAllowedForUrls policy list. This allows the authentication handshake without opening third-party cookies broadly across the device fleet.
Scenario 3: Network-level proxy or content filter
Some districts run content filtering at the network layer, not the browser layer. In this case, browser settings alone will not solve the problem. The IT team needs to whitelist the MagicSchool authentication endpoints at the proxy or firewall level. Providing the specific domain and the context — SSO token passing, not general tracking — helps IT prioritize correctly.
Directional time note: Diagnosing this as a password or server error and working through generic support channels typically takes several hours to days. Identifying it correctly as a third-party cookie conflict and applying a browser-level exception typically takes under ten minutes — if the device policy allows it. For managed devices requiring IT, a well-framed ticket with the specific cause can reduce resolution time from days to roughly one IT cycle.
Where This Fix Does Not Solve the Problem
Applying a cookie exception in the browser solves the authentication loop for most individual educators on personal or semi-managed devices. It does not address every scenario.
Fully locked managed Chromebooks often prevent users from modifying any cookie settings. The exception needs to be deployed at the Admin Console level, which requires IT access. A teacher cannot fix this alone on a district-issued device with full policy enforcement.
School networks with strict SSL inspection sometimes break the authentication redirect chain even when cookies are permitted. In these cases, the MagicSchool sign-in domain may need to be added to a separate SSL bypass list — a less common but real scenario in high-security district environments.
Student-facing MagicSchool access introduces a separate layer of complexity. Student accounts on Google Workspace for Education often operate under more restrictive policies than staff accounts. If student access is part of the plan, the cookie exception and domain whitelisting need to be confirmed at the student organizational unit level, not just the staff level. Assuming staff access works means student access also works is one of the more common rollout mistakes.
And one more edge case worth naming: if the login loop persists even after the cookie exception is applied, check whether the school’s Google Workspace admin has restricted third-party app access entirely. Some districts require explicit admin approval before any external tool can authenticate via Google SSO — regardless of cookie settings. That is a separate approval process in the Admin Console under Security → API Controls → App Access Control.

Why Identity Management Is the Real Gatekeeper of Classroom AI
Most EdTech adoption conversations focus on features, pricing, and curriculum alignment. The conversation that actually determines whether teachers can use a tool on any given Monday morning is the authentication layer — and it is almost never discussed during tool selection.
MagicSchool is not unique in this. Any AI tool that uses Google SSO in a school environment will face the same potential conflict. The pattern repeats across districts: an administrator approves a tool, teachers try to log in, a percentage of them hit a silent loop, and the tool gets labeled as unreliable before the authentication cause is ever identified.
SSO Conflict: What Each Stakeholder Needs to Know
TEACHER / EDUCATOR
If login loops with no error message → suspect third-party cookie block before assuming password or server fault. Check browser cookie exceptions first.
IT ADMINISTRATOR
Add MagicSchool domain to CookiesAllowedForUrls policy before rollout. Confirm student OU settings separately from staff. Check API access controls if SSO approval is required.
INSTRUCTIONAL DESIGNER / EDTECH LEAD
Include authentication testing in the pilot checklist. A tool that passes curriculum review but fails at login never reaches the classroom. Test SSO under the actual student and teacher account policies, not personal accounts.
The friction is not technical complexity. It is the gap between the person who approves the tool and the person who tries to use it on a managed device under a policy they did not configure and cannot change.
Want a practical EdTech rollout checklist?
Get the AI Tool Access Checklist for School Environments
Covers SSO testing, cookie policy checks, student vs. staff OU differences, and the IT ticket language that actually gets resolved faster. Practical, not theoretical.
The Practical Takeaway
A login loop with no error message is not a password problem. It is your school’s identity policy doing exactly what it was configured to do — and the fix is a cookie exception, not a support ticket.
